DEF CON attendees remind us just how easy it is to bypass laughable voting machine safeguards. At least they got the mainstream media to cover this issue for once.
Over the past two days, all major US news outlets breathlessly reported that hackers in Las Vegas needed little time to expose the security flaws of several types of voting machines this weekend. While it is certainly nice to see the mainstream media cover election integrity issues more than once every four years, anybody following the topic, as WhoWhatWhy routinely does, was hardly surprised that the hackers were so successful.
How do we know? Because, in anticipation of what happened at the DEF CON hacking conference, WhoWhatWhy spoke to many of the leading election integrity experts to get their thoughts on the event.
Most of them expressed hope that the hackers would raise much-needed awareness of the vulnerabilities of US voting machines.
Some of the experts we spoke to ahead of the event expressed concerns that, should the hackers fail to breach the machines, it would give people a false sense of security. It turns out that they did not have to worry about that — at all.
“…all of the studied systems possess critical security failures that render their technical controls insufficient to guarantee a trustworthy election.”
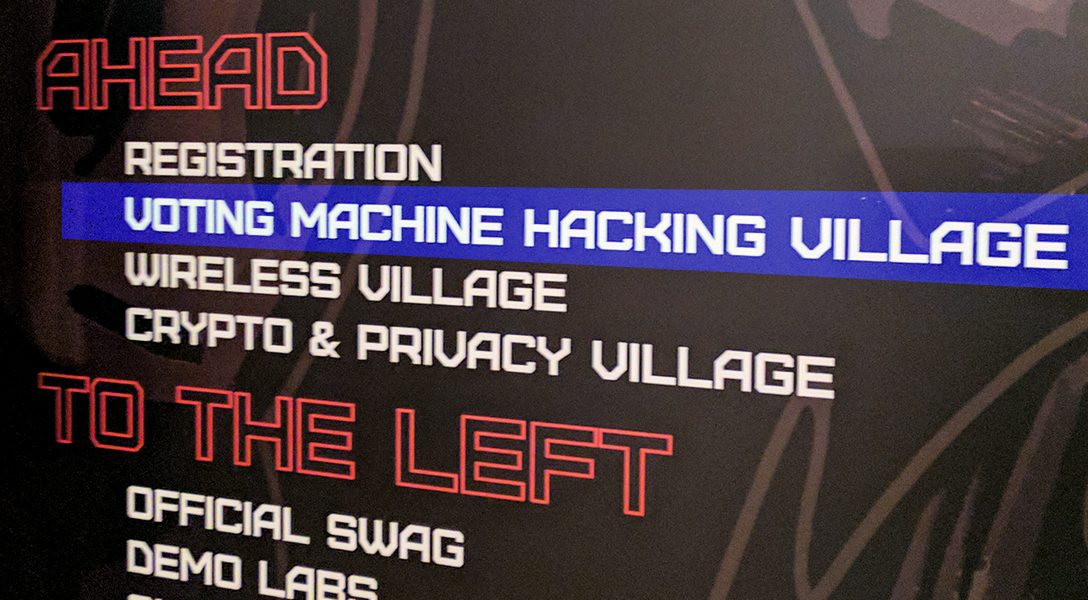
Hackers wasted no time decimating voting-machine security when they were invited to take a swing at more than 30 “real voting machines, used in past elections and to be used in future elections” obtained by the event’s organizers for the convention’s inaugural “Voting Machine Hacking Village.”
Doug Kellner, co-chair of the New York State election board, lauded DEF CON’s “commendable” effort.
“We can never be certain that our systems are completely secure,” Kellner told WhoWhatWhy. “If hackers expose vulnerabilities, that is a positive development that can motivate election officials to address those issues.”
Some election officials went one step further, travelling to DEF CON “to hack the very machines they use in their jurisdictions to run elections,” according to Harri Hursti, the Finnish cybersecurity expert who helped spawn the Voting Village.
“This was their first opportunity to take a look themselves into the machines — machines they were forced to use and manage, but were prohibited to study — and find answers to their own questions and learn the truth about that equipment,” Hursti told WhoWhatWhy.
But not every public official shares this curiosity, or advocates total transparency. Some would rather keep quiet about these security failures in order to preserve the American public’s faith in the integrity of our democratic system. Nevertheless, computer security experts and election integrity activists generally agree that raising public awareness is the best means of motivating change.
Password in the #ESS #iVotronic svcsvc – they found it by googling at the #VotingVillage #DEFCON #defcon25 that machine in use in 18 states.
— Lulu Friesdat (@LuluFriesdat) July 30, 2017
https://twitter.com/thepacketrat/status/891404141108621312
Hackers in attendance successfully infiltrated the DRE touch-screen systems and voter poll books almost immediately, according to a DEF CON representative. It took a mere 40 minutes for an attendee “with no prior knowledge” of the system to hack the Express-Pollbook 4000, which is still deployed in Ohio. Within 90 minutes, hackers “gained complete remote control” of the AVS voting terminal, a “glorified laptop running Windows XP” that was decommissioned by the Virginia election board in 2015. The country’s “worst voting machine” is host to a slate of vulnerabilities, including “physically unprotected” USB ports, hilariously simple default encryption keys and passwords (“a-b-c-d-e” and “admin,” respectively), and wi-fi capabilities that beg hackers to come right in.
Hackers had varying degrees of success circumventing the security of the Sequoia AVC Edge, the iVotronic, and a TSX machine, which are collectively employed by more than 800 municipalities nationwide, according to Verified Voting. The same machines are rolled out statewide in Nevada and Louisiana (Edge); Washington, DC and South Carolina (iVotronic); and Alaska, Georgia, and Utah (TSX).
Some computer experts, like J. Alex Halderman, entered the weekend with tempered expectations. The prominent University of Michigan computer science professor, well-regarded for his work in the field of election-tech security, said that, while the event was “a nice way to raise awareness of the issues,” he “suspect[ed] that it’s way too short a time for anybody to demonstrate interesting hacks.”
Election security consultant Neal McBurnett, who was also prepared for a lackluster showing, cautioned against jumping to conclusions. “If nothing new comes out of this, it is NOT a sign that all is well,” said McBurnett, noting that DEF CON’s “very ad-hoc” setting was “no substitute for a proper red-team engagement, with sufficient time, access to system code and documentation, etc., all of which are of course available to a well-supported adversary.”
In hindsight, the biggest takeaway here seems to be that meager resources are no barrier to a determined, capable hacker.
“Once you’ve discovered that the front door is unlocked and that there’s no alarm system and no security cameras, how much does it matter whether the windows are unlocked, too?”
Under the industry-friendly Digital Millennium Copyright Act, this sort of “white hat” hacking would have been impossible just a few years ago — or at the very least, illegal — as the copyright-protection law deemed voting machine software strictly off-limits without official supervision.
And as Hursti explained, the official studies that were allowed under the DMCA were defanged by “restrictions on what the participating researchers were allowed to try…which obviously would not exist for criminals.”
But the DMCA was amended in the wake of the ongoing Volkswagen emissions scandal to allow decreased restrictions on unsupervised hacking of vehicle software, and incidentally, election tech, provided it was done in the name of “good faith security research.”
Mike Kiniry of election software provider Free & Fair credits these restrictions for voting companies’ unearned public trust.
“The fact that very few [voting systems] have been demonstrated to be hackable is mostly a case of it being literally illegal until fairly recently,” said Kiniry.
Computer scientist Daniel Zimmerman said relaxed restrictions, combined with the media frenzy surrounding Russian voter database infiltration during the 2016 presidential election, was “a ‘perfect storm’ for setting up a public hacking event like DEF CON put together.”
Reflecting on the weekend’s accomplishments, Hursti said DEF CON “established that people with no previous knowledge of voting machines, without even being provided proper tools, can still learn to hack the machines within tens of minutes or a few hours.”
While DEF CON findings may prompt jaw-dropping among the uninformed, those familiar with this technology’s frighteningly inadequate security could only shake their heads in agreement. Ohio’s landmark EVEREST study, which examined voting systems from some of the largest players in the election tech market, including ES&S, Premier, and Hart InterCivic, came to the conclusion that “all of the studied systems possess critical security failures that render their technical controls insufficient to guarantee a trustworthy election.”
For this very reason, experts have fervently espoused physical paper ballot trails — a feature lacking in many DRE systems — which can be accessed to verify election results, should there be any cause for doubt.
Philip Stark, an associate dean of mathematical and physical sciences at UC Berkeley, went so far as to pronounce the hype surrounding the event “a little overblown,” given the vulnerabilities already brought to light by state-sponsored evaluations like EVEREST, as well as the published findings of academics like Halderman and Hursti. Hursti’s successful hack of a Florida county’s voter systems, all the way back in 2005 — depicted in the documentary Hacking Democracy — prompted the state of California to order its own comprehensive security review.
Stark, who also serves as an advisor to the federal Elections Assistance Commission, anticipated that DEF CON hackers would “find new flaws.” But he said he was not worried about further shaking the confidence of the American public in the country’s voting systems: “Once you’ve discovered that the front door is unlocked and that there’s no alarm system and no security cameras, how much does it matter whether the windows are unlocked, too?”
While the mainstream media discusses election integrity issues very infrequently, WhoWhatWhy is at the forefront of covering this crucially important topic. As we have demonstrated time and time again, US democracy is under constant threat — both from external forces as well as from elected officials. We have written extensively about voting machine vulnerabilities, voter suppression, gerrymandering, unlimited money in politics and much more.
Now, in a non-election year when everybody else tends to forget about this issue, we plan to do the opposite. We want to step up our coverage even more. To do so, we need your support. If you are an expert in this area and would like to help us, please contact the Election Integrity Unit. If you want to provide financial assistance, please get in touch with our founder and Editor-in-Chief Russ Baker. For our part, we promise to continue to shine a light on any threat to our democracy.
Related front page panorama photo credit: Adapted by WhoWhatWhy from voting machine (subfinitum / Flickr – CC BY 2.0).