Georgia Voters — Out of Country, Out of Luck?
The State’s Overzealous (and Ineffective) Plan to Stop Election Hackers
With non-US internet users barred from at least one of the electoral websites in the ultra-hot state of Georgia, it may be Georgians abroad — not would-be hackers — who are locked out.
If Georgia is fishing for election hackers, maybe it should consider opting for the more precise rod-and-reel method, rather than a dragnet.
Election and cybersecurity experts are still scratching their heads after Buzzfeed reported that Georgia’s election division was blocking any and all foreign access to its online voter registration page — including to its own citizens abroad — in a move that may wind up hurting Georgia voters more than it protects them.
And amid an election year where the country, and the world, is watching Georgia, this takes on heightened significance. Stacey Abrams, the Democratic attorney general, will become the nation’s first-ever black female governor if she prevails over Republican Brian Kemp.
In his day job as secretary of state, Kemp oversees elections.
The logic behind Georgia’s defensive internet strategy is that blocking foreign IP addresses will prevent hackers, who would presumably be operating overseas, from embedding themselves in the state’s election infrastructure. Websites like Netflix employ similar devices to restrict content to particular territories in order to ensure that users can only view titles that have been licensed to their region.
The particulars are tricky and technical, as is often the case in the dry field that is election administration. But if time isn’t taken to untangle them and weigh their consequences, legitimate voters may be left in the cold while the state publicly waves its victory banner.
Related: Who Ordered Destruction of Data That Could Have Proved Georgia Election Rigging?
A Touchy Subject
.
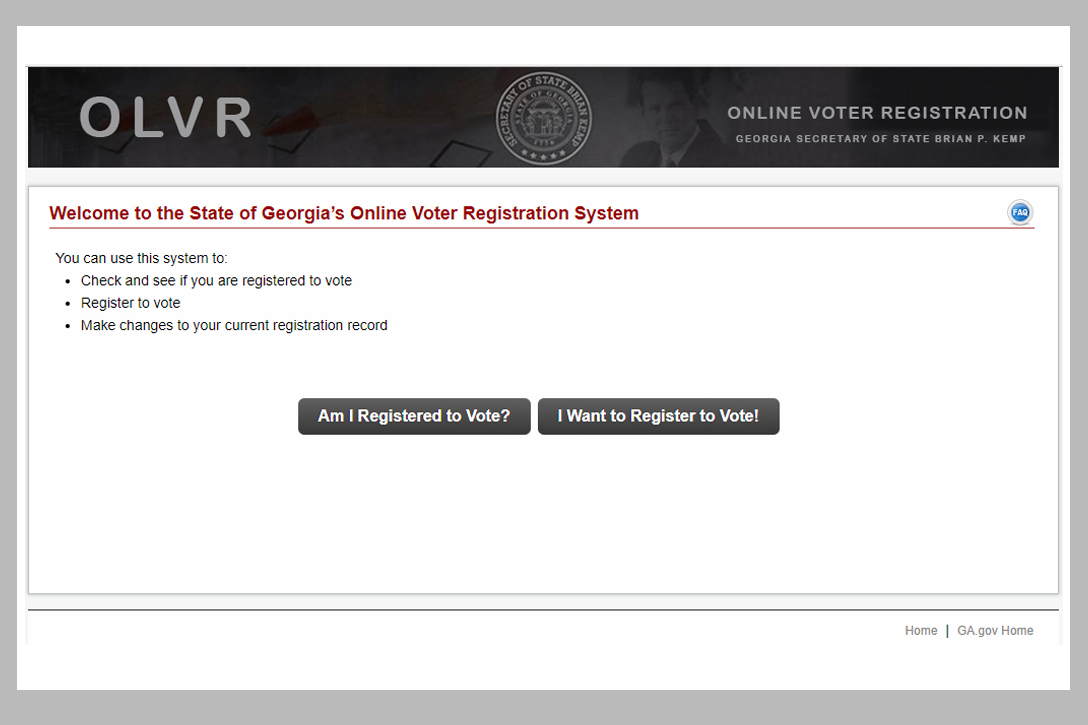
When asked to comment on the news that even Georgians abroad were being locked out of the state’s voter registration website, Kemp’s press office claimed the original Buzzfeed report was mistaken and that the publication had confused the online voter registration site (OLVR) with the state’s “My Voter Page” (MVP), which is the portal used to apply for and electronically obtain absentee ballots. It was the latter site, they said, that had been cut off from overseas traffic.
The two sites “have different functionality,” a spokesperson for Kemp wrote in an email response to WhoWhatWhy. “Online voter registration has nothing to do with balloting.”
When asked to explain the practical difference between the two; specifically, how the blockage would affect Georgia’s residents and soldiers overseas; and why either site should be walled off at all, Kemp’s office requested more time to respond but never did.
For the record, one WhoWhatWhy editor tried accessing both sites from overseas and had no problem accessing the MVP but could not get onto the OLVR. Several other WhoWhatWhy foreign correspondents reported the same issue.
But let’s give Kemp the benefit of the doubt and assume that the OLVR is still, as his office claims, accessible (which does not appear to be the case), and that overseas users were able to register through the other state-run website. That would still at the very least indicate that the state appears to be stripping those users of convenient ballot access by rescinding MVP access.
Every self-respecting internet junkie knows the obvious workaround to this hurdle: just cover your tracks with a proxy.
In other words: While the right to vote in Georgia is supposed to be accorded to registered Georgia voters no matter where they are located on the planet, those voters who wish to vote but live on foreign soil may be unable to do so because of as yet unexplained limitations imposed by Georgia state election officials.
While Kemp’s press office couldn’t say exactly how many voters would be affected by this internet-access problem, it did say that 1,097 “absentee voters requested ballots and indicated that they were overseas” during last May’s election.
The closing lines of a statement obtained from the press office displayed defensiveness in the face of mounting criticism:
It is completely hypocritical for critics to bash Kemp for not doing enough to prevent foreign interference while simultaneously questioning security protocols to prevent foreign interference.
It is hypocritical to bash Kemp for ‘voter suppression’ by reducing access to foreign IP addresses on a system that he created to enhance voter engagement.
After being routinely scolded for what some see as consistent mishandling of his election oversight duties, one would think Kemp and his staff might have thicker skin by now.
Related: Georgia Officials Knew Equipment Was Vulnerable — Before the 2016 Election
Medieval Defenses for a B-52 Bomber
.
Apparently contradicting the previous assertion that the original Buzzfeed report was in error, an email from the SoS spokesperson bluntly stated that the “online voter registration system is inaccessible to entities utilizing non-US IP addresses” and has been “since last year.”
The spokesperson went on to insist that “military and overseas voters can still access voter registration forms, absentee ballot applications, and other important voting information” through the state website as well as “numerous third-party websites. This traffic is not blocked from MVP since we are nearing the UOCAVA [Uniformed and Overseas Citizens Absentee Voting Act] balloting period.”
All in all, this seems like a convoluted way of saying, You got it all wrong. We didn’t block voters from registering last week… we did it a year ago.
Either way, this is like digging a moat to hold off an aerial assault.
After all, as every self-respecting internet junkie knows, there is an obvious workaround to this “sophomoric technical security response,” as one cyber expert described it: Just cover your tracks with a proxy server. That might sound complicated to the uninitiated, but even a cyber novice could figure it out in no time with a quick Google search or two.
“I’m noticing that State officials are becoming very … wary of charges that they’re not being serious about possible foreign attack,” Stewart told WhoWhatWhy.
The SoS, however, seems to believe this simple process won’t be worth the effort for some.
“It is clear that some bad actors will not utilize VPN (virtual private network) to get around this configuration,” said one spokesperson. “They will move on before they take the extra time.”
But Berkeley professor and election audit expert Philip B. Stark noted that “even slightly sophisticated hackers … try to anonymize their location.” He even admitted to using a VPN himself.
Not only are experts like Stark confident Georgia’s unusual defensive tactic will fail to halt the return of the Russians; they worry it will actually restrict access for ordinary citizens who lack the technical acumen to get a proxy and don’t want to deal with all the hassle.
“It would do nothing to dissuade anyone with even the slightest technical capability. It’s much more likely that they will block legitimate users who end up at garbled URLs for the PDF,” Joseph Lorenzo Hall, chief technologist at the Center for Democracy, wrote in an email exchange with WhoWhatWhy.
The question here is: Is blocking these bottom-rung hackers worth the cost to Georgia voters?
The SoS office claims that because voter registration PDFs remain online, Georgians will still retain full ballot access, with one caveat: They just have to call their office if they encounter an issue on the blocked site — which experts suggest is more probable than possible — and someone will talk them through the process of downloading and printing the document.
But Hall says issues could still persist, especially for Georgia’s less tech-savvy voters.
“They don’t understand what a PDF is or what a URL is,” wrote Hall. “They may type it in incorrectly, copy and paste it poorly, or [do] any number of things” that will leave them staring in frustration at an error message. At that point, Hall said, “any possibility of trying to navigate to the PDF more naturally will fail because all other pages are blocked for non-US IP addresses.”
For those who know the pains of providing IT support for computer-illiterate family members, this may sound familiar.
To make matters worse, Hall says, there is “more surgical and temporary” blacklist technology available that the state could have used, without risking indiscriminate disenfranchisement.
These alternatives “either use information about past reputation of a given IP address” or something called “dynamic information,” which can scan the web for attacks in real time and add the responsible IP to a list of bad actors.
This approach has been shown to work in Vermont.
Vermont’s secretary of state, Jim Condos, told WhoWhatWhy that his state blocks specific IP addresses coming out of “known or suspected” national threats — like Russia, China, and North Korea — as well as any others flagged and forwarded their way by the Department of Homeland Security or the Multi-State Information Sharing & Analysis Center.
Condos, the elected president of the National Association of Secretaries of State, said the notion that foreign automatically equals bad is simply “a false premise.”
“I mean, where does it stop?” he asked. “Do they stop at Canada? Do they stop at Mexico? Do they stop at England?”
Related: GOP State Officials Are the Real Threat to Democracy
Hanlon’s Razor
.
The SoS representative said the state opted for the blanket method based on the advice of “private sector security vendors” after discussing the decision “with federal offices at multiple agencies.”
But MIT political science professor Charles Stewart III, a member of the Caltech/MIT Voting Technology Project, suggested the controversial decision may have been reactionary — a consequence of the endemic skittishness among election officials who find themselves facing increased scrutiny.
“It’s not a defense by any means, but I’m noticing that state officials are becoming very … wary of charges that they’re not being serious about possible foreign attack,” Stewart told WhoWhatWhy. “If I had to guess, my sense is someone pointed out that there are possible bad guys from overseas who could get into our VR [voter registration] system, and one of the ways of putting a kibosh on that is to block foreign IP addresses; maybe not thinking through the implications of it.”
“Whenever something like this comes up the first thing I think of is Hanlon’s Razor,” said Stewart.“‘Never attribute to malice what can be explained by stupidity.’”
Related front page panorama photo credit: Adapted by WhoWhatWhy from woman at computer (Dépt. Arts UVHC / Flickr).