A WhoWhatWhy investigation shows that, for the last 16 years, Georgia has either been ignoring or misinterpreting one of its own rules on storing election data.
This week, election officials across Georgia are going to break a rule in the election code and tamper with potential evidence as they prepare for December’s runoff and special elections, just as they have since 2002.
The rule in question mandates the maintenance of the internal memory of voting machines for one month after an election. The problem is that Georgia has an election schedule that makes that rule essentially impossible to enforce. Runoffs, like the one coming up on December 4, often happen within a month of the main election.
WhoWhatWhy investigated whether or not it was possible to both maintain the internal records of voting machines and prepare them for use in a new election. Both state and county officials say yes.
Six computer security experts and two lawyers who study election systems disagree.
What’s at stake here is more than a scheduling error in Georgia’s election code: it is the security and transparency of the election itself.
Why It Matters
.
“The problem with the Georgia system is that you simply don’t know,” computer security expert Rich DeMillo said, referring to the legitimacy of an election.
DeMillo, currently a professor of computer science at Georgia Tech, has had a leading role in technology and security at Hewlett-Packard, Bell Communications Research, the National Science Foundation, and the US Department of Defense.
It’s a well-established fact that Georgia’s election system is vulnerable to cyber attacks at many levels.
It has been public knowledge since at least 2006 that the state’s voting machines are vulnerable to hacking.
This is especially troubling since the voting machines do not have a paper trail and cannot be audited. In other words, it’s impossible to know with full certainty whether the outcome of any Georgia election actually reflects the votes cast, DeMillo said.
What the state could do — and has never done — is perform a forensic examination of its voting system to search for changes made by an outside party or for irregularities that could have affected the vote.
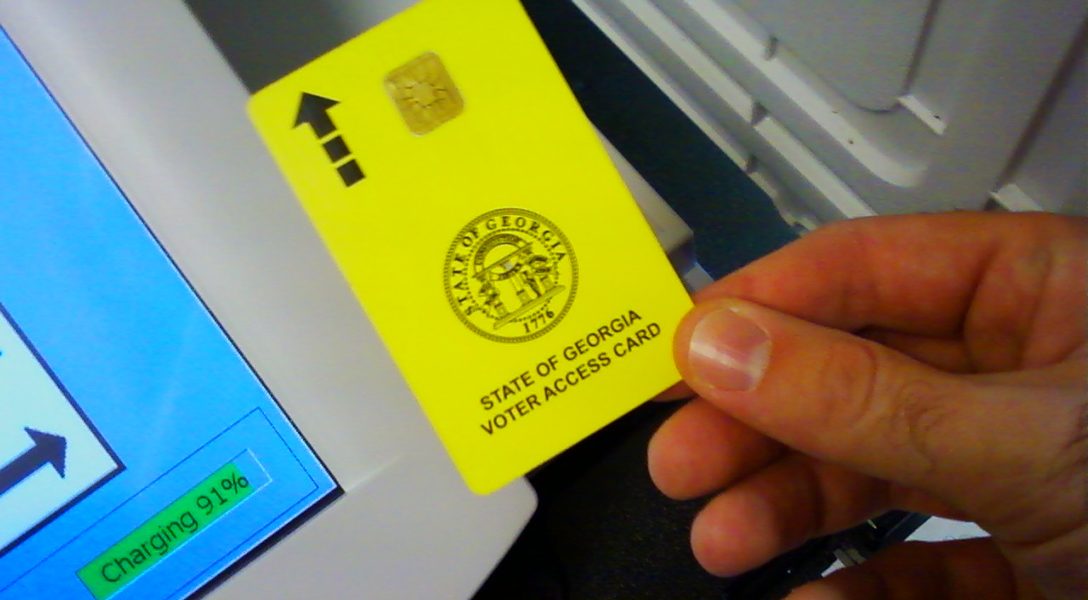
Messing with the machines or the voter cards is just one way in, but one that has the potential to be extremely effective. By gaining access to just one voting machine, a hacker could modify vote totals for the entire state.
Standing outside of Fulton County’s election preparation center, election security expert Logan Lamb explains one of the many ways Georgia’s election could be hacked. Access to just one machine in one county could change votes for the entire state.
Gaining access to a machine is not difficult. WhoWhatWhy found poorly secured voting machines in Fulton County ahead of early voting for this year’s midterms, and the “tamper-evident” seals used to lock the machines are easily picked. Once opened, the key to access the memory card slot is commonly available online, or easily picked (it takes under 10 seconds), according to a Princeton University study.
“An attacker who gets physical access to a machine or its removable memory card for as little as one minute could install malicious code,” according to that same study.
Logan Lamb, a computer security researcher, shows how easy it is to bypass the “tamper-evident” zip-ties used to seal election machines. Research has shown it takes just over a minute of physical access to download malicious code onto a voting machine.
If votes were to be changed, it could be done in a way that wouldn’t be noticed, according to DeMillo. Recounting votes wouldn’t catch the error because the votes recorded on each memory card could have been rewritten, and the malicious code could still be in the computers the state uses to count the votes.
Looking at memory cards, or even reading the vote totals saved on the internal memory of DRE machines would likely be ineffective for the same reasons.
It appears that the best option Georgia has to ensure the accuracy of the election is to perform a forensic audit of the election system, including each voting machine, to search for irregularities or any bad code.
Even if a bad actor were suspected of messing with the election and a forensic examination were to be done (transparently and with opportunity for public review), there is no guarantee that evidence of a hack would be found. It is possible to write malicious code that covers its tracks, so anybody inspecting the machines wouldn’t be able to tell that something had been changed.
But the examination is still worth doing, according to DeMillo, because a hacker could make a mistake, be sloppy, or use an attack vector that doesn’t affect every machine.
To do that, the state would need to preserve all of the voting machines. The Coalition for Good Governance, currently involved in litigation against the state for issues of election security, issued a letter to the defendants demanding that they preserve the DREs. If their demand is ignored, the coalition will take up the issue in court today.
Part of the coalition’s argument is that candidates in the midterms can still contest the election, and that the information on DRE machines should not be changed before they can be reviewed. The letter outlines alternatives for conducting December’s election, including using paper ballots.
“It is essential that all November 6 electronic data on the voting machines not be altered by loading runoff ballot programming on the machines,” said Marilyn Marks, the group’s executive director. “Nor should the voting machines be deployed to unsecured locations like polling places. The law and common sense require that the electronic records be fully and diligently preserved at least until any potential election contests are resolved in the Courts.”
Think of the DREs like evidence in a criminal investigation. If a gun was possibly used in a murder, the police aren’t going to let that gun get wiped down, let it be carried around and left in public places, or allow it to be fired again. That gun will be in a plastic bag in a storage locker until it can get tested for evidence.
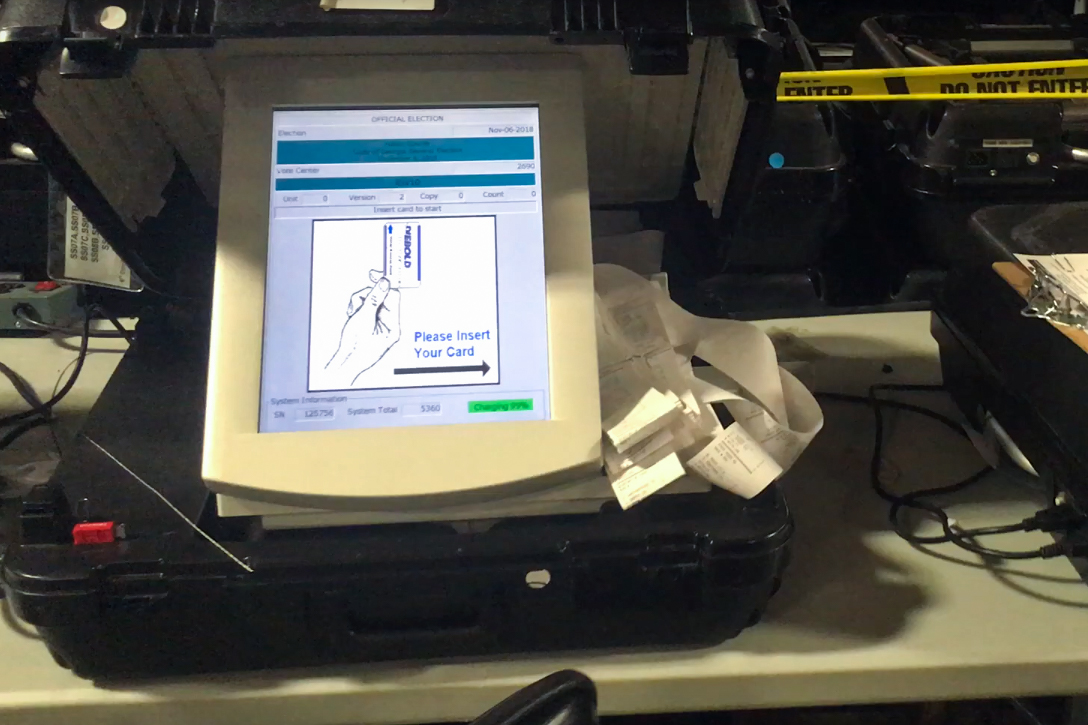
State officials knew when they adopted the DRE voting machines in 2002 that they did not have a paper trail. That is the same year that the State Board of Elections wrote a rule, part of the state election code, mandating that the internal memory of voting machines must be maintained for 30 days after an election. That’s the elections version of preserving evidence for an investigation.
Few election officials know about this rule, seem to understand it, or follow it.
The Rule
.
The rule in question is pretty simple. It reads:
The election results, ballot styles, ballot images, and other information for each election stored in the internal memory storage of each DRE unit shall be maintained for a minimum of one month following each election after which time the results may be erased provided that there are no election contests pending concerning such election.
In summary, data on each DRE used in an election should be preserved for 30 days, and maybe longer if there is an election contest.
But that’s not happening in the real world. Two weeks after Election Day, counties are getting ready to start “Logic and Accuracy” testing. The state has certified the election and once ballot layouts are finalized (proofs were sent to counties on Saturday), counties will start to program the voting machines for the runoff election.
The question is, how can internal memory be maintained and, at the same time, altered for the new election?
Candice Broce, press secretary for the secretary of state, issued a statement to WhoWhatWhy, writing in an email that, “Elections officials comply with this rule in its entirety.”

Matt Bernhard, a computer security expert and Ph.D student in computer science at the University of Michigan, said that, “in computer science terms, this is utter nonsense, because [the] internal state for a computer changes every time you turn it on.”
To fully preserve the internal memory of a DRE, the machine would need to be stored for a month, with no updating of software, uploading of new ballots, or testing with new memory cards. Just stack the machines in a warehouse and leave them off. Anything else would probably be breaking the rule, if it is read in its strictest sense.
The only possible out, according to Bernhard and other experts, is if the rule is interpreted to only refer to election results, which take up very little space on the memory. Since the oldest files are deleted first, it is very likely — though it cannot be guaranteed — that all of the results from a recent election will be preserved.
Indeed, a statement from Broce suggests that the secretary of state interprets the rule to only include election results.
“Using the machines in a run-off does not affect the storage of previous election results in internal memory,” Broce wrote in an email. “It is false to claim that the only way to preserve data is not to use the machine.”
But that leaves out “ballot styles, ballot images, and other information.” Just looking at election results would not necessarily reveal anything. If a machine had been tampered with, it would store the faulty results, too.
The Legal Take
.
WhoWhatWhy independently consulted with lawyers from two public-interest law firms. Their opinions were consistent. The county election officials are breaking the state’s election rule.
Stacey Leyton, legal partner at Altshuler Berzon, wrote in an email that there were two ways the DREs used in the November 6 election could be used in the December 4 runoff and follow the state’s rule. Neither have been done before, nor are likely now.
First, the machines could only be used “if elections officials were able to create an exact image of the internal memory of each voting machine prior to loading the programming for the runoff.”
This process is called mirroring. Its purpose is to capture more information (like the DRE’s programming) more accurately than simply copying the DRE’s memory, according to Camille Fischer, a government transparency lawyer with the Electronic Frontier Foundation.
WhoWhatWhy asked the director of registrations and elections for Fulton County, Richard Barron, if he or his staff knew how to do this.
“We don’t do that,” Barron said, and he doesn’t know how to do it, either. It would either have to be done by the secretary of state’s office or the vendor, he said. WhoWhatWhy asked Janine Eveler, director of registrations and elections for Cobb County, the same question and was similarly told that only the machine vendor could make an exact copy of the internal memory of a DRE machine.
Harri Hursti and Logan Lamb, both cybersecurity researchers with expertise in election systems, said this process is onerous. Simply put, it would require soldering a piece of computer hardware to the DRE’s motherboard. Then, a cable would be used to connect the DRE to an external computer and begin downloading. That step alone could take 3–10 hours per machine.
Fulton County alone used almost 2,000 voting machines in the 2018 midterm.
“The alternative, to comply with this rule,” Leyton said, “would be to use paper ballots in the runoff.”