The White House shot down a critical election security bill ahead of the November midterms under the guise of federalist principles. Will our democracy pay the price for this dogmatic approach to states’ rights?
From racial segregation to environmental destruction to voter suppression, the concepts of “federalism” and “states’ rights” have a long-running association with some of the worst outcomes of American conservatism.
And we may soon add “endangering American democracy” to that list. These political philosophies are being invoked to sink a key election-security bill — at a time when midterm elections are being actively probed and prodded for weaknesses by potentially hostile nation-states.
The Secure Elections Act (SEA), which seemed poised to become a rare bipartisan slam-dunk, may not even make it to a vote now that the bill has been pulled from committee, reportedly under order of the Trump White House.
A White House spokesperson told Yahoo News that passing SEA “could violate the principles of federalism,” referring to the idea that states should remain sovereign over the federal government whenever possible and appropriate. These principles have long been the preferred ideological weapon for states and municipalities that feel — or claim — that the feds are infringing on their jurisdiction.
This is especially true in the realm of election administration.
“Secretaries of state [are], in general, resistant to any sort of federal mandates on elections,” MIT political science professor Charles Stewart III told WhoWhatWhy. But partisanship plays a role here as well, says Stewart.
“Over the last eight years or so, there have been elements of the Republican Party who just want to get the federal government out of everything having to do with elections,” he said.
Although the Constitution grants Congress authority over federal elections, states otherwise generally have a strong claim to this civic responsibility, although to what extent depends on how one interprets the following:
The Times, Places and Manner of holding Elections for Senators and Representatives, shall be prescribed in each State by the Legislature thereof but the Congress may at any time by Law make or alter such Regulations, except as to the Places of chusing Senators.
As always, though, we must ask: Is there a legitimate constitutional concern here, or are federalism’s core tenets once again being bastardized to sandbag a bill that experts say is desperately needed to ensure that states can protect their elections from tampering?
A January review of the bill written by the director of Harvard-Kennedy’s Cyber Security Project — a former cyber policy director at the Department of Defense — suggests the latter.
[The Secure Elections Act] does not command states to act in specific ways, it does not hijack election administration from counties, states, or municipalities, and it limits the federal government’s role to advising and empowering state and local jurisdictions to run their proverbial railroads.
SEA would ramp up election security by incentivizing states to beef up their procedures and offering Department of Homeland Defense resources, like security clearances and improved information-sharing, to election officials.
Related: Are Americans Beginning to Care About Election Integrity?
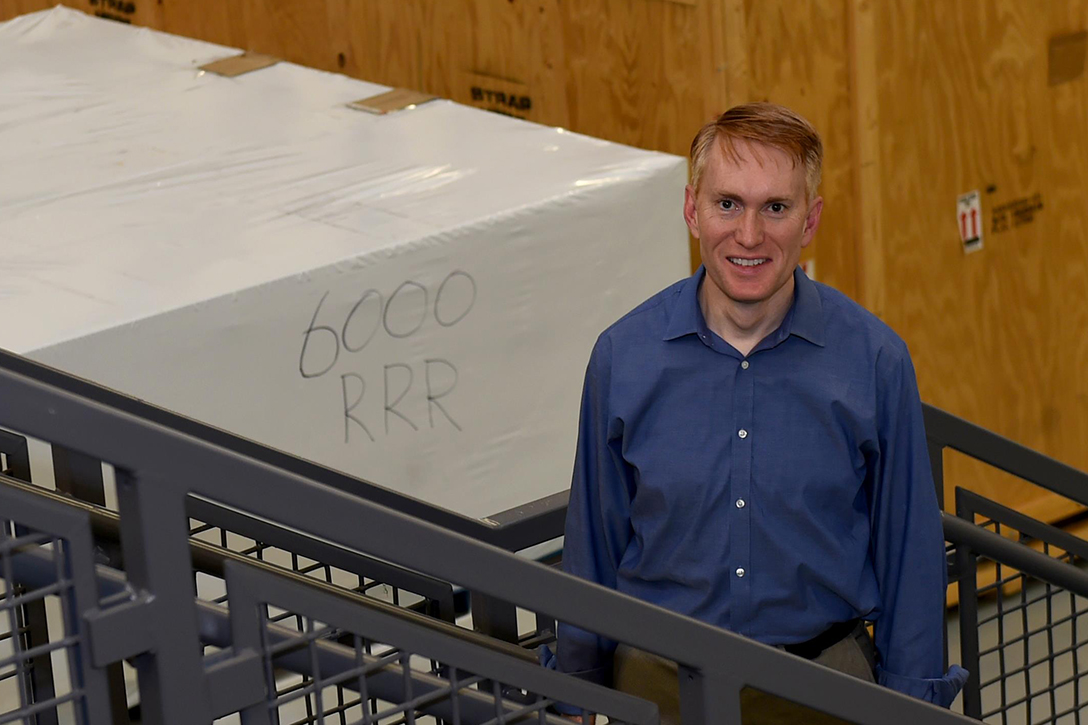
The bill’s lead author, Sen. James Lankford (R-OK), also pushed back against accusations of overreach, making explicitly clear that SEA incentivized — but did not mandate — certain practices that would better secure elections. In addition, he says that it’s the responsibility of the federal government, not the states, to protect Americans against foreign threats.
Given Republicans’ prominent role in fighting to keep big government out of the states’ business, it’s worth noting that they were playing a significant role in moving this bill forward. Consider Lankford: he isn’t just a Republican — he’s a consistent ally to the president with a 90.8 percent “Trump Score” from FiveThirtyEight. Yet his co-author is Sen. Amy Klobuchar (D-MN), and the bill’s sponsors include such strange bedfellows as Sens. Lindsey Graham (R-SC), Kamala Harris (D-CA), and Susan Collins (R-ME).
A Toothless Bill
.
Lankford denies this blow was fatal for the legislation. An email newsletter from the senator said, “After a year of work and edits, my bill … continues to make positive progress toward full consideration in Congress.”
That year brought considerable changes to the Secure Elections Act in order “to accommodate the Republican leadership” so that it might receive the necessary votes to pass through the Senate, according to Klobuchar — much to the chagrin of election reform advocates, who say these concessions cost the bill its teeth.
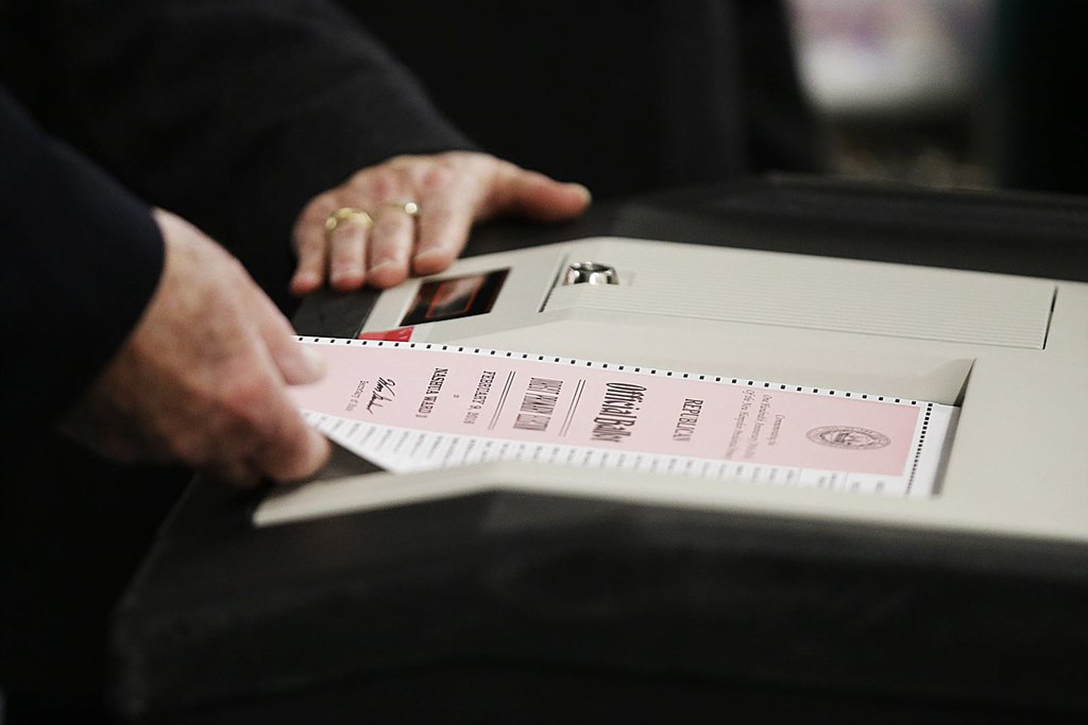
The Center for Democracy and Technology asked Sens. Klobuchar and Roy Blunt (R-MO) — chairman of the Rules Committee, where SEA’s markup session was scheduled prior to being shelved — to reinstate a scrapped provision requiring that post election audits be counted “by hand and not by device.”
Without this precise language, the CDT warned, the law could allow for “inferior forms of election auditing [that] will on balance be a net negative.”
This sentiment was echoed by California Secretary of State Alex Padilla in his own letter to Lankford.
But while technologists and election reform advocates consider such safeguards absolutely critical in order to verify elections, their administrators say some — like the provision requiring states to engage in a particular form of auditing known as a risk-limiting audit (RLA) — are problematic.
Stewart said it appears that “there are elements of the bill that will never be acceptable to secretaries of state.”
“In particular, the parts that would mandate post-election audits [and] the use of paper” ballots, he said, “are going to get at least twenty secretaries to dig in their heels.”
These holdouts, he said, “are more likely to be Republican.”
Unfortunately for anyone hoping to see this bill made into law, Stewart says these same folks also happen to “have the ear of the White House.”
Jim Condos, Vermont’s secretary of state, told WhoWhatWhy that he himself had initial misgivings about the legislation — concerns he says he voiced during a conference call with the federal Elections Assistance Commission — since the bill “appeared to be a further federal intrusion into states’ rights and states’ oversight of the elections process.”
However, considering Condos hadn’t even reviewed the language yet at the time, he — unlike the White House — now admits that judgment may have been premature.
But while this particular concern “receded a little bit” once he did his homework, Condos said others quickly sprung up in its place.
“What I was concerned about,” he said, “was the prescriptive nature of the audit language.”
Just as Stewart suspected, the RLA was a main point of contention.
Condos said the bill’s language concerning audits was “so specific that” that it could wind up stifling innovation and bar administrators from performing alternative forms of election auditing “that might actually prove to be even stronger or better” than the RLA.
Related: New California Law Strikes Blow to Election Audits
In fact, Condos seems quite confident that Vermont’s audit protocol is actually superior to the RLA in regards to the degree of statistical confidence it offers.
His other concern over the RLA provision is simply that not every state is up to the task. “Only a handful of states,” he said, are properly equipped for RLAs, in which auditors pull select ballots from the batch according to the order in which they are received (say, the 35th, the 105th, etc.) to be manually verified against the final vote vote count in order to statistically verify the election’s outcome.
Vermont — along with “the vast majority of states,” according to Condos — does not count its ballots in such a fashion — or in any real sense at all. Instead, he says, they’re all lumped together in a bin and put through the ballot scanner.
“Here’s the thing,” said Condos. “I’m not saying that risk-limited audits are bad. In fact, I think they are good — if you have the systems in place to do them.”
But Condos says that if the federal government is going to insist on telling states how to run their own elections, they should at least foot the bill.
“If they [are] gonna starting telling us exactly the type of audit that they wanted, if they [want] to get into the type of equipment they want us to use, then they should take over the cost of that. Otherwise it’s an unfunded mandate.”
But if the bill’s defenders are correct, there is no mandate in this legislation.
Though the National Association of Secretaries of State (NASS) hasn’t announced a firm position on the Secure Elections Act, Maria Benson, a spokeswoman for the organization, told WhoWhatWhy via email that both the collective organization and several individual members had their own concerns regarding “certain provisions of the bill including definitions, implementation guidelines, [and] nomination processes.”
The battle over this bill is just the latest in the long-standing give-and-take between centralization and state sovereignty in the US which has the states’ side ringing the alarm bell.
We saw this play out just last year: After the world learned that foreign agents had targeted election systems in every state, the Obama administration placed elections within the mission parameters of DHS by designating them “critical infrastructure,” putting them in the same bracket as hospitals, power grids, and nuclear reactors.
In the eyes of Georgia’s head election administrator, Secretary of State Brian Kemp (R) — a lightning rod for election controversy who’s currently in the running to become the state’s next governor — this was “blatant overreach.”
Connecticut Secretary of State Denise Merrill (D) has said letting a federal body into state elections could lead to transparency concerns among voters.
Obama’s DHS Director, Jeh Johnson, pre-empted critics with a defense similar to the one Lankford made for his bill, saying the designation did “nothing to change the role state and local governments have in administering and running elections” and insisting the security analysis his department offered was completely voluntary.
Unfortunately, any hope that this might cool tensions was dashed after Kemp sent a letter to Johnson after claiming to have linked DHS IP addresses with attempted breaches of their election firewalls.
Johnson’s response that this was not a hacking attempt, but merely a standard information request from the server by a DHS employee cutting-and-pasting data from Georgia’s elections website into an Excel sheet, did not satisfy Kemp — who asked President Donald Trump to investigate.
While the NASS wasted no time coming out against the designation, if Condos felt as strongly as Kemp did, he was more diplomatic about it — perhaps because someone first had to explain to him and the rest of the nation’s election officials what this actually meant moving forward.
Following the designation announcement, he says that for “probably the next six months” his fraternity of election administrators continued peppering the feds with questions about what changes this move would bring, though it was starting to seem like wasted effort.
For the better part of a year, they “really weren’t getting good answers,” said Condos, who feels the transition between the Obama and Trump administrations may have contributed to the poor communication. He says it wasn’t “until early summer of 2017” that the secretaries came to fully understand “what the critical infrastructure designation would mean and what resources would be provided to the states.”
Condos insists their communication “has really improved since then.”
One likely contributor to this improvement was the formation of an inter-agency, inter-departmental working group one NASS press release described as a “first of its kind collaboration between federal, state, and local officials to secure elections.”
Drawing from the ranks of DHS, NASS, the federal Election Assistance Commission, the National Association of State Election Directors, the Election Center, and the International Association of Government Officials, the Election Infrastructure Subsector Government Coordinating Council (EIS-GCC) is designed to facilitate information and resource sharing between the various concerned parties.
For all their reluctance to get in bed with the feds, this development suggests that states and municipalities remain open to some degree of collaboration. Asked whether the EIS-GCC represented the outer limits of how far he would feel comfortable with continued federal involvement in their elections, Condos said it “would be wrong” to make any assumptions at this point.
“It would be like asking me if I’m ever going to run for governor,” said Condos. “I would never say ‘Never,’ but that’s not my intention at this point.”
As long as the DHS remains a valuable source of information for the states, Stewart says, the objections will be easier to ignore.
“Those voices,” he says, “Are not as loud as they once were, and not nearly as persuasive.”
Admittedly, it’s hard to see the truth in that, given the current uncertainty over SEA.
But given the magnitude of the threats facing our elections, let’s hope he’s right.
Foreign Cyber Threats
.
According to the Moscow-based ZecurionAnalytics, Russia spends up to $300 million annually on their cyber warfare division and employs more than 1,000 “cyber troops.”
But we shouldn’t just be bracing ourselves for the Russians; Trump’s notoriously hawkish national security adviser, John Bolton, said the administration is also concerned about cyberattacks being perpetrated by Iran, North Korea, and China — the latter dwarfing them all with its $1.5 billion cyber budget and 20,000 cyber troops.
Fortunately for American voters, the Pentagon’s $7 billion cyber budget outpaces any other superpower, lending some credibility to the idea that it may actually be equipped for this fight. However, considering hackers have already succeeded in penetrating some of our most essential infrastructure already — not just election servers, either, but the US power grid — Americans probably shouldn’t rest too easy just yet.
Related: Hackers Eviscerate Election Tech Security…Who’s Surprised?
And of course, who’s to say whether those resources will necessarily translate into a successful cyber shield? After all, the US has a long and storied history of making the false assumption that big budgets and superior technology would be enough to defeat its opponents.
But that aside, any confidence this lends regarding federal protections should not necessarily be extended to the individual states, especially when legislation that would enable greater collaboration between them can’t even get a committee markup, let alone a Senate vote.
Hearing that the IT safety nets of states like Alaska and Montana are facing off against geopolitical giants like Russia and China, it’s easy to assume the worst will inevitably come to pass.
But is it feasible that these states might actually be able to hold their own in this David vs. Goliath scenario?
“To a certain extent, yes,” CDT President Joseph Lorenzo Hall told WhoWhatWhy. “Nation-states have particular goals and are not going to spend more resources than they need to.”
Hall said that “even the most simple cybersecurity controls — for example, two-factor authentication — can provide a substantial increase in protection.” Although basic, these safeguards can force would-be attackers to stick out their necks by eliminating the possibility of a remote attack and forcing them to get up close and personal.
Thus, it seems clear to many both within and without the legislative branch that Congress should make it a priority to ensure that states are adequately funded to put these and other measures into place.
While states do have $380 million coming their way to upgrade their election systems, the Brennan Center for Justice says its “not nearly enough.”
Bear in mind: That amount has to be divided up among 50 states. Some like California, which made off with the most of any state ($34.5 million), will come out far better prepared than other, less populous states like Alaska and Montana, each of which will have to make due with $3 million.

According to Brennan estimates, eleven states are still running elections on paperless systems — the bane of transparency advocates, who say the lack of a physical paper trail makes it impossible to guarantee the validity of a final tally. Without additional financial resources, the policy institute says these states will be unable to replace them with more trustworthy machines.
Pennsylvania, for instance, needs $36.9 to $65.6 million more than what’s already been set aside in these provisions if it wants to replace its paperless machines. For some, like Minnesota, the dollar amount doesn’t even matter so long as in-state budget battles continue preventing them from accessing their funds in time for the November elections.
Better Days?
.
This windfall makes more sense when you realize that these funds are just unspent leftovers from the Help America Vote Act that have been gathering dust and cobwebs since 2002 — a simpler time, when hanging chads were widely considered the biggest threat to our democracy.
Ironic that while the stakes seem so much higher, the political will to address them seems to be backsliding. Looking back today, the idea that Congress could scrape together nearly $4 billion to improve democratic practices seems like a pipe dream after this SEA debacle.
And that’s too bad, since those HAVA scraps may be the last federal dime these states see for a while, seeing as Senate Republicans recently shot down an additional $250 million allocation.
Not to say that passing HAVA was a painless effort. Stewart, who says he “was involved in the peripheries” of HAVA’s writing and passage, said that “opposition from state officials” came close to killing the legislation “many times.”
You can probably already guess why.
These officials took issue with HAVA’s provisional ballot mandate, and its prohibition of certain mediums — like mechanical voting machines and punch cards — was a sticking point for state officials, said Stewart. The same goes for the Voter Registration Act, which he said “came really close to being killed because of concerns about federalism, as well.”
Here’s hoping that the holdouts recognize what’s at stake here. After all, November is just around the corner. And Americans should probably assume that foreign powers are going to come after their ballot boxes with everything they’ve got.
Related front page panorama photo credit: Adapted by WhoWhatWhy from US Navy / Chips (CC0)



