A magazine-length, must-read story of hackers, leakers, democracy advocates, spies, cops, banks, lobbyists, WikiLeaks, the future of the Internet…and quite possibly of our democracy.
Humble Beginnings
As an Internet muckraker, Brown had a penchant for pulling the string wherever it might lead. He was quick to take on established interests and orthodoxies, picking apart cherished truths if just to see their adherents scowl. Eventually this predilection led him to become bound up with a group that made Time Magazine’s list of 100 Most Influential “People” of 2012: the hackers’ collective known as Anonymous.
The media, in referring to Anonymous, usually suggest that it is far more concrete an entity than it actually is, with “members” and a chain of command. In fact, Anonymous has no more “organization” than a group of strangers with shared interests in, say, a Harry Potter chat room. As a result, responsibility for any action attributed to Anonymous is, by its very nature, diffuse and untraceable.
What originally united “members” was immersion in a Net-centric subculture that prizes personal liberty and anonymity, if simply to exercise the right to prank people online. From this amorphous origin evolved a network of rebellious scofflaws and bored teenagers, along with a share of idealistic activists. The potential to mobilize these individuals to act in concert for a commonly defined goal is what gives Anonymous its power. Over time, a few of these digital rapscallions came to share a belief that this power can, and should, be used as a democratizing force.
Some trace the “group’s” beginning back to 2003 on the imageboard 4chan.org—a forum for discussing Japanese comics. “These were just kids … interested in arcane Japanese web culture and, of course, pictures of boobs,” says Tim Rogers, author of a D Magazine cover story on Brown’s Anonymous links. “They harassed people in online role-playing games and indulged in other forms of online pranking.”
Then, as now, users (now often known as “Anons”) would communicate using Internet Relay Chats (IRCs), a now ubiquitous staple of the Internet. For laymen, an IRC can best be understood like any other chat room (among other things, enabling live text messaging, privately or within groups, as well as data transfer capabilities). Whether for digital pranking, discussing the Japanese anime craze, or coordinating resistance to repressive regimes, the ability to communicate and organize via IRCs has been apparent since the chats first appeared in the late 1980s. For example, during the 1991 “August Putsch” by Communist hardliners against Soviet president Mikhail Gorbachev, IRCs were used to disseminate information during an internal media blackout.
What eventually became Anonymous’s IRCs didn’t begin as places to plan ‘hacktivism’. They were simply digital hangouts where computer geeks could gather to discuss modes of pranking in online gaming communities. And as anyone who’s ever surveyed a comment forum can attest, anonymity gives users the nerve to say things that, for fear of reputational damage or social stigma, they otherwise never would. This admittedly mean-spirited ethos was a staple of the culture in IRCs.
“One of the things that Anonymous was at that time was an outlet [for Anons] to vent a little,” explains Gregg Housh—a once-active member of Anonymous and confidant of Brown’s. “Sociopaths seem to fit naturally into that world,” Housh says. “[It] wasn’t about activism.” As an aficionado of such activities in the online role-playing game Second Life—allegedly creating swarms of digital dildos with which to barrage other people’s online houses until their computers crashed—Barrett Brown was able to parlay his way into the often-sophomoric Anonymous fraternity.
Not So Anonymous
As a freelance writer by day and online prankster by night, Barrett Brown found himself at home among his new cohorts in the Anonymous IRCs.
Although Brown is routinely referred to as a “self-proclaimed Anonymous spokesman,” he’s conceded in an interview with NBCNews on March 8, 2011 that he was no such thing: “I can’t speak on behalf of Anonymous, because there’s no one who can authorize me to do that.”
Brown was dubbed a spokesman for the collective because he was one of a few willing to speak on record, using his real name, about Anonymous activities to the media. Brown is what some Anons refer to, almost admiringly, as a “namefag.” As Tim Rogers explains: “The term is not intrinsically derogatory. It just means that one has publicly identified oneself with Anonymous, using the name on one’s birth certificate.”
“I liken him more to an embedded journalist or media liaison,” explains a Kevin Gallagher, a close friend of Brown. The two met in New York City during the summer of 2012 at the HOPE9 Conference (HOPE stands for Hackers On Planet Earth), and have remained close. Since his arrest in September, Gallagher says, “[Brown] calls me on average once every two weeks.”
According to Gallagher, Brown wasn’t much of a hacker. He was “unabashedly lacking [the] skills” to access protected databases or participate in the big activities coordinated through certain Anonymous IRCs. Brown simply acted as a go-to source for media when big Anonymous operations were conducted. It was a dangerous position to put oneself into, and few did.
Ironically, Anonymous itself had security issues. “Toward the end of his freedom he seemed to be growing disappointed with the people in Anonymous,” Gallagher told WhoWhatWhy. “[Brown had] seen Anonymous become infiltrated [and] co-opted, and people choosing to become informants.”
Indeed, FBI infiltration and cooptation were able to sow discord within the ranks of Anonymous. This can be seen in the case of “Sabu”, an alleged ringleader of LulzSec—a highly active subgroup of Anonymous that coordinated many of the larger, illegal actions—turned government informant. In August of 2011 he pled guilty to 12 criminal charges, and began working with the FBI to trace other LulzSec members.
After the Sabu matter exploded publicly, many members of LulzSec were arrested in the following months, and the inner circle of hackers comprising Anonymous began to fragment. But that disruption did little to lessen the underlying esprit—a strong sense of individual empowerment that came from an ability to act collectively and yet still maintain personal privacy. That diffusion of power and knowledge hindered many attempts at infiltration by law enforcement.
Simply put, few Anons actually know anything about one another, so there are few opportunities to rat each other out. It’s a setup that the Mafia would appreciate. With this inherently hard-to-dismantle structure, or lack thereof, Anonymous continues to make its presence felt: on February 11 of this year, the state of Alabama’s website was hacked in retaliation for allegedly racist state immigration legislation. Personal information that was being stored by the state on 46,000 citizens was collected and supposedly deleted.
From Dennis the Menace to Robin Hood
In the latter half of the past decade, Brown, a University of Texas-Austin dropout, worked as a freelance columnist producing copy for the likes of New York Press, Vanity Fair, Huffington Post and The Onion. Channeling H.L. Mencken, Brown co-authored a 2007 book titled Flock of Dodos: Behind Modern Creationism, Intelligent Design, and the Easter Bunny. Matt Taibbi, known for his stinging critiques of the financial industry in Rolling Stone, had this to say about it: “With their painstaking attention to historical detail and amusingly violent writing style, Brown and [his co-author] Alston have given the religious right exactly the righteous, merciless fragging it deserves.”
Brown’s commentary had always been attuned to civil liberties, the erosion of Constitutional rights, what he saw as an inept or complicit media structure, and the impact of the Internet on all of these issues.
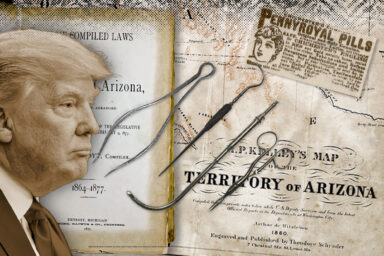
As one might expect from this pedigree, Brown began writing quite favorably about WikiLeaks and pro-public-accountability forms of digital protest. Brown claimed to have been in contact with a number of the activists who in 2008 launched the first coordinated action associated with Anonymous: Operation Chanology. It began with a bizarre interview that appeared on YouTube, showing actor Tom Cruise extolling Scientology that was leaked by a disaffected former church member. The Church claimed copyright violation, asserting the video was solely intended for internal distribution to church members and threatened YouTube with litigation.
When YouTube removed the video, Anonymous posted their own video decrying censorship. Then Anonymous launched a sustained campaign of (the now familiar) denial-of-service (DDoS) attacks against Scientology websites, together with prank calls to Scientology offices worldwide and barrages of “black faxes” that tie up receiving machines and deplete their ink reserves. Anonymous’s brand of mischievous activism was born.
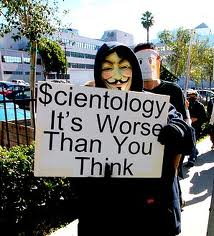 The Church of Scientology fought back by publicly naming one of the publishers of Anonymous’s response video in a civil suit. That publisher was Gregg Housh. Since he had already been outed, Housh was then willing to assume the role of a go-to spokesperson (or “namefag”) for those seeking answers about the hacker collective.
The Church of Scientology fought back by publicly naming one of the publishers of Anonymous’s response video in a civil suit. That publisher was Gregg Housh. Since he had already been outed, Housh was then willing to assume the role of a go-to spokesperson (or “namefag”) for those seeking answers about the hacker collective.
“I remember when we first started [targeting Scientology],” recalls Housh. “I got to this weird point only a few weeks into [the operation], where some of the teenage ex-scientologists had started convincing me of just how evil this organization was… We started thinking about this as an actual cause. From then on it just kept going.”
Housh is describing his transformation into a “moralfag,” jargon for Anons who see Anonymous as a tool for doing good and for holding powerful people and organizations accountable to “the people.”
“I was told very clearly that we needed to stop ruining [Anonymous’s] ‘bad name,’” Housh claims, referring to the immature, joker ethos that pervaded the collective at that time. “I was staring at my screen, and just thought, ‘God damn it. This is wrong.’”
All this took place before Housh and Brown met. What happened next, though, would thrust Brown into the spotlight, where he would eventually find himself in the crosshairs of the federal government.